FamiGuard Support: Monitor Devices with Others' Permission.
Have you ever used Telegram before? Telegram is a popular chatting app, loved by many people for how fluid it is in showing chats and stickers. In addition, telegram is also a very secure platform, which also encrypts chat content to protect users' privacy. Although telegram works very well and focuses on protecting user privacy, there are some cases of Telegram hacking happening all around the world.
Most of the people who monitored into some accounts usually didn't take anything rather than monitor everything. By monitoring, they can see the contacts, the chats, and all the details related to those two. If you also want to know how to monitor Telegram, we've already prepared some materials for you.
Table of Contents
Part 1: How to Monitor Telegram - 3 Ways
To monitor telegram, you need to prepare some things first. However, the items are definitely connected to the methods, so the more complex the technique is, the more sources you will need. And talking about the methods to monitor into Telegram, here are a few examples:
1. Session Hijacking
Difficulty:
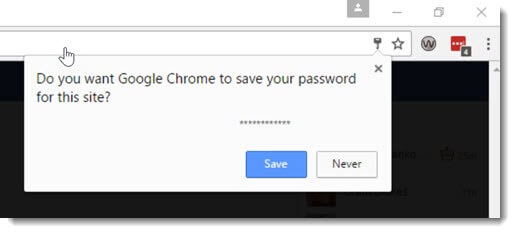
Session hijacking involves stealing a user's session ID to gain unauthorized access to their Telegram account. This can be done by intercepting network traffic or by exploiting vulnerabilities in the user's device.
How monitors use session hijacking to monitor Telegram accounts
When a user logs in to Telegram, the server assigns them a unique session ID. This ID is used to identify the user during their session. If a cybercriminal is able to intercept the user's network traffic, they can obtain the session ID from the cookie. With the session ID, the cybercriminal can impersonate the user's session and gain unauthorized access to their Telegram account. Finally, The cybercriminal can use the session ID to access the user's messages, contacts, and other sensitive information.
To protect your Telegram account from session hijacking, What should you do?
Use a secure connection: Always use a secure connection when accessing Telegram, such as a VPN or SSL connection, to reduce the risk of interception.
Keep your device and software up to date: Keeping your device and software up to date can help protect against vulnerabilities that may be exploited by monitors.
2. Phishing Email
Difficulty:

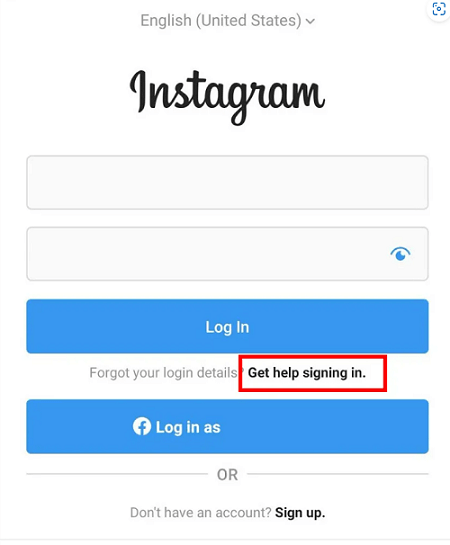
In this step, the telegram monitor becomes more serious. This is when you actually have the full intention to get someone's data. So, always be cautious while doing so. Phishing emails are emails that contain several convincing pieces of information that lead a target to input their username along with the passwords. The emails have to be as convincing as possible to spark interest. Here is how it works:
Firstly, The cybercriminal sends a phishing email to the user, posing as a legitimate source, such as Telegram support. And the email may contain a link that leads to a fake Telegram login page, designed to look identical to the real one.
Secondly, The user enters their login credentials on the fake login page, believing it to be the legitimate Telegram website.
Finally, The cybercriminal receives the user's login credentials and can then log in to their Telegram account.
3. Man-in-the-middle attack
Difficulty:
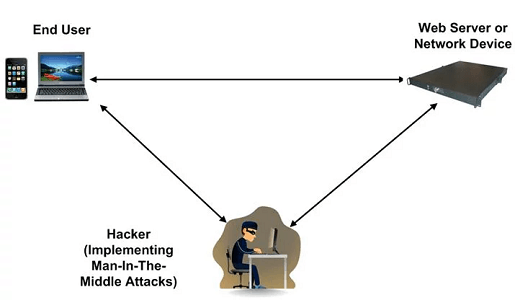
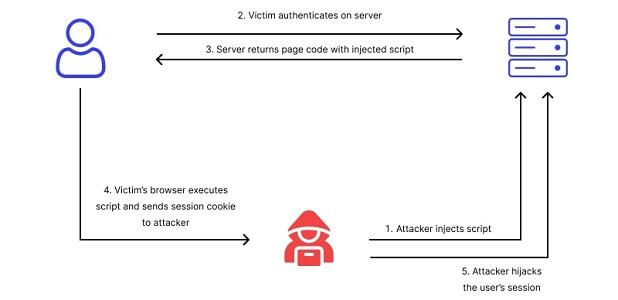
In a man-in-the-middle attack, the cybercriminal intercepts the communication between the user and the Telegram server. This allows the cybercriminal to steal the user's login credentials and gain unauthorized access to their Telegram account. However, this method requires some techniques, which is difficult for general people! If you are interested in this method, we will still tell you how it works!
Firstly, When a user logs in to Telegram, their login credentials are sent to the Telegram server over the internet.
Secondly, If a cybercriminal is able to intercept the communication between the user and the server, they can obtain the user's login credentials.
Thirdly, With the login credentials, the cybercriminal can access the user's Telegram account and view their messages, contacts, and other sensitive information.
Finally, The cybercriminal may also be able to modify the messages or data sent between the user and the server, allowing them to manipulate the conversation or steal additional information.
To protect your Telegram account from MITM attacks, What should you do
Verify SSL Certificates: Before logging in to Telegram, make sure to verify that the SSL certificate presented by the server is valid and matches the domain name you expect.
Be Cautious of Public Wi-Fi: Avoid logging in to Telegram on public Wi-Fi networks, as these networks can be insecure and increase the risk of interception.
Part 2: How to Monitor Telegram Easily
We have just discussed three methods of Monitoring Telegram, including Session Hijacking, Phishing Email, and Man-in-the-middle attack, but all three methods are too specialized and difficult to implement. So, to easily monitor into someone's Telegram account and monitor his or her activities, you can also use some monitor apps. Having these apps at your fingertips will make the task much easier and quicker.
1. FamiGuard Pro
Difficulty:
Rate:
Of all these telegram-monitoring apps, FamiGuard Pro is the best. All you need is physical access to the target phone and install this app, then you can easily monitor someone's telegram account and see who they are chatting with and what they are chatting about!
Here is how to use it:
Step 1: Create your account for FamiGuard Pro for Android
Step 2: Download the FamiGuard Pro for Android App from the given address
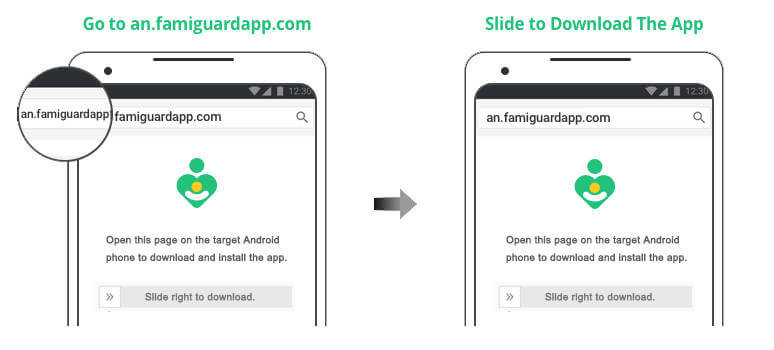
Step 3: Set it up on the target smartphone.
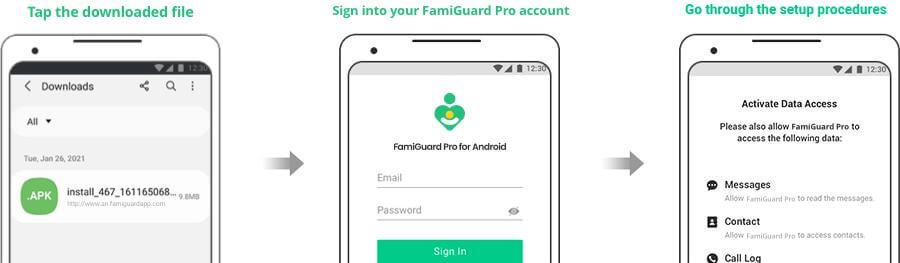
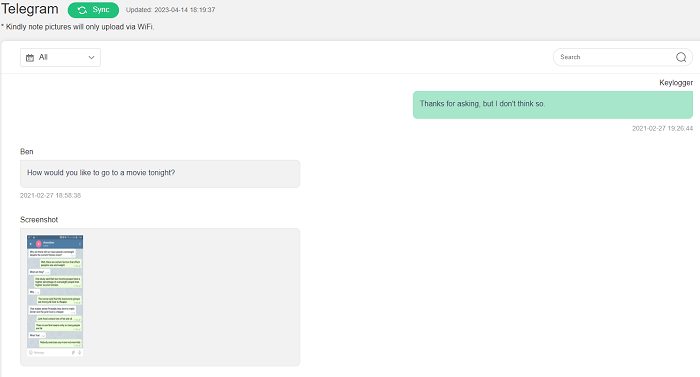
Step 4: Log into FamiGuard Pro for Android online dashboard, then choose "Social Apps" and "Telegram" to monitor all kinds of activities on target phone

Amazing Features of FamiGuard Pro for Android
-
Monitoring Social Media Apps: Viewing messages or pictures on WhatsApp, Tiktok, Facebook, Telegram, Instagram, Snapchat, Viber, WeChat, and more
-
Keylogger Feature: It has a keylogger feature that records everything typed on the keyboard.
-
Remote Control: Recording phone calls, capturing screenshots and taking photos in control mode
-
Phone File Viewing: With FamiGuard Pro for Android, you can monitor messages, call logs, contacts, photos and browser history on the target phone at any time
2. eyeZy
Difficulty:
Rate:
eyeZy is also a reputable monitor app that's known for its features. It can read all the things inside the target phone, and it doesn't matter whether the app is encrypted or not. eyeZy will make the monitoring job runs more smoothly since it also works discreetly. After installing the app on the target phone, you can basically access someone's Telegram account from where you stand. See their pics, calls, chats, videos, and other files directly from your phone.
3. Hoverwatch
Difficulty:
Rate:
The next option you can use to do Telegram monitors is Hoverwatch. Again, this is a monitoringing app that's valuable in terms of features. You can see the details of Telegram here, including all the media files sent in the chats. Aside from Telegram, the app also supports various chatting apps as well.
Part 3: Why Do People Monitor Telegram?
Different people have different reasons for monitoring into telegrams, some for monitoringing, others for spreading malware or viruses, extortion or harassment, etc. In the following part we will discuss these reasons in detail.
Kids Monitoring
Generally, the reason people do monitoring is for monitoring like kids monitoring. Parents usually choose to monitor into children's Telegram to make sure that their kids are not exposed to dangerous online materials. As you may know already, the internet is full of everything. The lack of boundaries makes it possible for the kids to access something way higher than their age. So, the parents can monitor their kid's online activities directly from these apps to make sure that everything is going fine.
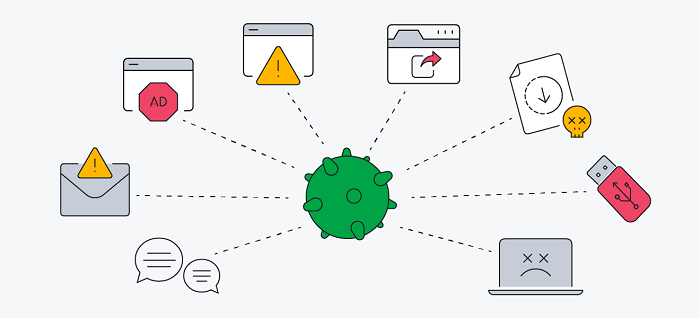
Spread Malware or Viruses
Monitorers can spread malware or viruses through your Telegram account by sending malicious links or attachments to your contacts or groups. Once a user clicks on the link or downloads the attachment, their device can become infected with malware or a virus. The malware or virus can then spread to other devices in their network.
Blackmail or Harass
Telegram can be used for extortion or harassment through threats, demands for money or otherwise. Monitorers may use the personal information they've obtained through your account to make their threats seem more credible.
By Tata Davis
An excellent content writer who is professional in software and app technology and skilled in blogging on internet for more than 5 years.